PO_License_Draft as of October 9.
For the rationale, see my video at https://www.youtube.com/watch?v=vTsc1m78BUk
PO_License_Draft as of October 9.
For the rationale, see my video at https://www.youtube.com/watch?v=vTsc1m78BUk
The canonical version of this document is at http://perens.com/static/AMSAT/Election2020.html . Please distribute it widely until September 15, 2020. We need to get it in front of all AMSAT members worldwide.
Last year, Bruce Perens K6BP wrote to you to recommend the election of new directors to the AMSAT board, to remedy severe problems with the organization. Two new directors were elected, but the then-incumbent board has never allowed them to function as directors. The main means used to disenfranchise the new directors were that AMSAT stopped having board meetings, so that the new directors can not make any motions or participate in any meaningful way. And information that would usually be given to directors was withheld from the newly elected ones.
If AMSAT members send additional new directors to the board, they will break this logjam, because there will be enough new directors to call a board meeting. The candidates we recommend are:
Many volunteer non-profit directors never learn a critical skill of democracy: how to deal with opposition. Opposition are not the enemy! They are just people with different opinions about how to run the organization. But an unskilled board will treat opposition as evil against their own good.
The new directors, Michelle Thompson W5NYV and Patrick Stoddard WD9EWK were vocal critics of the AMSAT leadership before they ran for office. Rather than work with the opposition, the AMSAT board started an expensive legal process against them. The membership then, to the incumbent’s great distress, sent the same people to the board as new directors! Which led to more lawyers and more expense. The total got to $18,000 in legal fees that should have gone to Amateur Satellites.
This was not a wise decision by the AMSAT board. They could have worked with the opposition, rather than spending money on lawyers and disenfranchising the directors whom the membership had elected to represent them. They should have read the election of these people as a signal from the membership.
So, this year AMSAT has the same problems reported a year ago. And this new one.
We are asking AMSAT members to fix this, by electing enough additional new directors to call a board meeting. AMSAT ballots are going into the mail as we write this.
Of course, besides fixing this administrative problem, the candidates have an agenda for the advancement of AMSAT. Dr. Bob McGwier N4HY was chief engineer of AMSAT and a board member during a better time for the organization, and is one of the creators of Software Defined Radio. He was one of the main architects of the Phase 4 satellite development, which would have provided a geostationary digital satellite for emergency communication, and regular ham activities during non-emergency times. This was a cooperative program with FEMA, part of the US Government, and FEMA’s vendor failed to build the satellite. Since then, space launch has become much less expensive and paths are open to AMSAT that would previously have taken government cooperation. Bob is the best choice to lead a new effort to go back to high-earth orbit with satellites that mix simple and accessable analog communications with innovative digital ones.
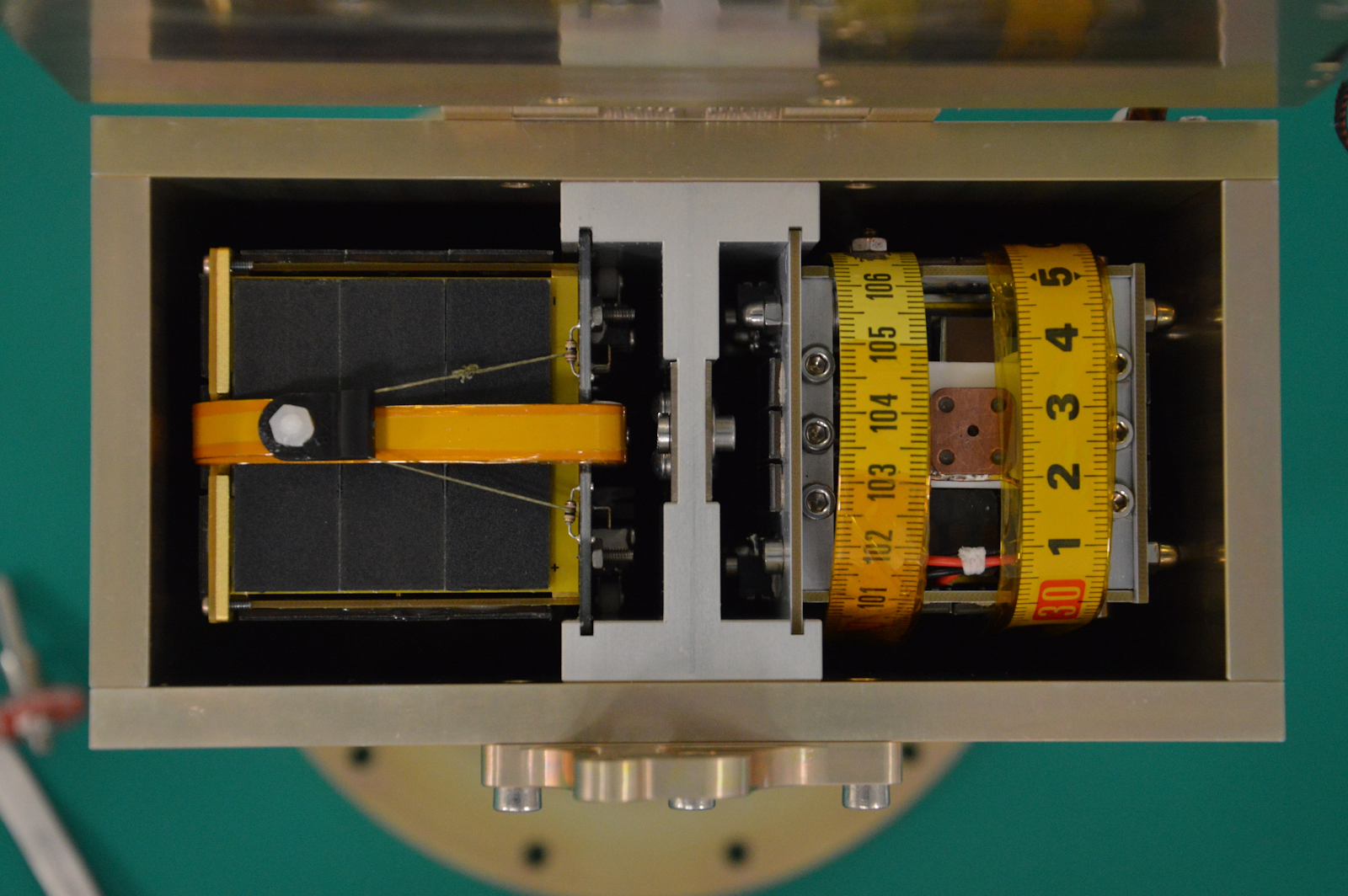
Howie DeFelice AB2S is a principal engineer for Intelsat General Communications, one of the creators of 50 Dollar Sat, the first PocketQube satellite, and a major contributor to the Phase 4 effort. Jeff Johns WE4B is an industrial quality expert and daily satellite operator. His expertise in Kaizen, a process to increase quality by involving all employees from top management to line assemblers, is essental to bringing AMSAT back to being a functional organization.
Please review the web statements of each candidate, and please vote for these candidates:
Signed:
Please write to bruce at perens dot com to add your signature.
You didn’t really even have to ask, but Bruce Perens stands in solidarity with Black Lives Matter. In 1997, I wrote non-discrimination provisions into the Debian Free Software Guidelines, which then became the Open Source Definiton. While they still stand, they have been constantly under attack.
My personal experience with prejudice comes from how I was treated as a neurologically handicapped child. But I am also subject to ageism, and most bigots do not consider me to be “white” because of my ethnic Jewish origin.
There has been some (fortunately unsuccessful) movement to cast aspersion on Open Source as the product of “old white men”. This is humorous because of the explicitly non-discriminatory nature of the work, and its origin within the Debian team, which has always been very diverse. Nobody should be rejecting anyone’s work due to their skin color.
Of late, I have come out with my discrimination story. It wasn’t color, but my speech and motor handicaps (then severe). On my first day in first grade, the teacher, on hearing me speak, took me by the hand and led me to another classroom, leaving me there. Back then, they called it the retarded children’s class. We’d have a nicer name for it today.
The first-grade teacher did this without having me examined, and if she told anyone in the school at all, the message wasn’t given to my parents. One of the things they did not do in that class was teach reading. Eventually my parents realized, from my description of my classmates, that something was very wrong. They got a lawyer.
Back then, around 1962, it was not accepted that handicapped students should be mainstreamed with the other children. Some thought we would slow the other students down and would be an unacceptable burden on the teacher. So, there were special classes or special schools where we could be out of the sight of the normally abled people.
This did not teach the normally-abled people to be accepting of the handicapped. We were different and scary, and they were given no experience in interacting with us.
Some children with motor deficits find handwriting difficult or painful. Those who do may develop a very good memory in compensation – as I have. I can still see that 1st grade teacher in my mind today.
Once I returned to her class, under the threat of a lawsuit and without her willingness, she was filled to the top and over with resentment. Every time I interacted with her, she explained to me, in front of the other children, that I did not belong in her class. The other children were actually told by this teacher that I was retarded, which set the way that I would be treated by many of my school peers all through the elementary grades. A lawyer-required test determined my IQ was 140 at the time, but this didn’t matter to my peers or the bad teacher.
While today handicapped students have Individualized Education Plans, and Accommodations that help them, nothing like that existed back then. It wasn’t until junior high school that I was placed in a class with a speech therapist. I had that for a few years and then they put me in rhetoric class every year through 12th grade. It didn’t fix my speech, but made me a good public speaker. Many people, on hearing me speak, would ask what country I came from.
My speech and coordination issues diminished on their own as I got older.
As an adult, I have had the police called on me at least once, simply for being someone who moves differently, and was thus considered a threat. I still get problems – especially in stores – because of the way I move, ranging from a woman screaming in terror (just because of the way I walked in, no kidding) to extra attention from security guards. If you move differently, people will consider you “creepy”. That word originates from “creeping”, moving abnormally.
The biggest damage from school wasn’t physical, though. Having such a difficult time didn’t help me with some of the subjects I should have been learning, and I am still innumerate by the standards of the computer and electronic engineers I work with today. In retrospect, some of the scenes I remember read as neurosis – one teacher even damaging equipment in his rage. I hope the classroom is better supervised today.
So, if you wonder why some of those students with darker skin don’t do as well, when they seem to be given the same school opportunities as you, it’s because they don’t really have the same opportunities at all. What they face, beside you in the school every day, impedes them.
Black lives matter, and unfortunately the place where Black people might need the most support isn’t what anyone is trying to fix right now. K-to-12 schooling is at least as important, and is as painfully underfunded, and as likely to let them down, as it was in 1962.
The solution so far, because we just can’t spend the money to have good primary schools, is to take away learning days to do testing and penalize the schools whose students test poorly. No surprise that these are often ones where the poor people live.
So, I hope we fix the police and other adult prejudice issues. But let’s please fix things for our kids. Otherwise, we will have another generation of underprivileged people, and another generation of people of all colors who have so little understanding of politics and the world that they vote for quick fixes and tyrants. Other countries, many poorer than ours, have achieved great primary schools that treat people fairly and educate them well. The USA can too.
For the past several months, I’ve been building a startup web business using the Crystal language and the Lucky web framework. This is a conscious decision to use bleeding-edge technology, thus all of the issues I’ve run into are my fault. The Crystal language is approaching its 1.0 release, and the Lucky framework has not yet announced any intention to make a 1.0 release yet.
The potential cost of my choices is high – my start-up will be soliciting millions of dollars of capitalization, starting this week. But I don’t believe my technical choices will be a significant problem for the business, other than requiring that I hire experienced Crystal programmers. They are available, in the US, Brazil, and elsewhere, but not as common as programmers for other languages so far.
The impetus for this choice was the power of the Crystal language and the potential of the Lucky framework built upon it to result in a more correct implementation. Crystal is a compiled, globally-optimized language with Ruby-like syntax and type safety. It provides type safety without type verbosity, inferring types rather than requiring declaration much of the time, and propagating type information throughout the program. It also has an extremely powerful macro language which has access to abstract syntax tree nodes within the compiler. This allows me, for example, to piece apart interpolated strings for translation, at compile time, without a significant run-time overhead. I don’t know of any other compiled computer language that would allow me to do this in a macro, using a documented API, rather than requiring me to write an external source-code processor.
The intent of Crystal and Lucky are that the programmer would have the syntactic grace and ease of writing in Ruby on Rails, with greater correctness, fewer run-time errors, and compiled-language speed. To an extent, the combination achieves this. I expected that there would be pain, due to the youth of the language and platform, and there has been.
Crystal and Lucky are not, in my opinion, ready for the inexperienced programmer. With over 40 years of programming experience, I have still faced challenges.
The power of Crystal’s macro language means that it is used extensively in packages as powerful as the Lucky web platform. Unfortunately, this means that your programming errors are reported where they occur somewhere in a macro expansion, rather than where you have made them – as you could expect were you calling into functions and methods rather than macros. The result is that error messages resulting from my use of Lucky are often simply indecipherable, yielding neither the location of their origin or, sometimes, even any information about the erroneous statement rather than some macro transformation of that statement. Since the macro system is a code transformation machine, its arguments are not naturally as tightly typed as the rest of the Crystal language. Achieving good error reports for Lucky may require manually-added code to more tightly check the arguments to every macro. Fortunately, the macro mechanism does provide the framework to do such checking, AST nodes yield type information and the file name and line number of where they originate. I don’t know if there is anything that the compiler developers can do to improve error messages regarding macro expansions.
For now, I have developed craft knowledge that helps me debug problems in macro expansions, but this has been a relatively steep learning curve.
Lucky also has some substantial bugs at this time, as would be expected for such a large and powerful system at this point in its development. About the worst that I’ve encountered is that the before and after functions used to manipulate data model properties and validate their correctness don’t happen in the right order, and can’t be put in the right order using the existing API, causing some errors to be set on the model before the programmer has a chance to correct them. For now, this requires that model code explicitly clear some errors.
There are a few problems in the existing Crystal language implementation, as well. The largest one that I have faced is that the union type system, which allows one to declare a type as a collection of other types, does not work as expected under the hood. My program has two models: Manufacturer and Product. A union type of Manufacturer | Product is changed, internal to the compiler, to their common subclass. Then, the compiler sometimes does type checking for the common subclass, rather than just Manufacturer and Product as I intended. For now, I’ve created a common subclass (closer to my models than the one the compiler would have had to pick) and declare that rather than a union type.
Another problem is that support for run-time debugging is incomplete at this time, and gdb has access to source code lines and the call stack, but can not examine some (or all) arguments and variables.
If you are willing to put up with these challenges, the Crystal language and the Lucky web platform offer more power than other computer languages I have experienced, more initial correctness, and the resulting code is fast. If you are in a hurry, or don’t have the chops to figure out cryptic errors, it’s not time for you to use Crystal and Lucky yet.
The canonical version of this appeal is at http://perens.com/static/AppliedIon/ , please re-publish it widely!
From Bruce Perens K6BP:
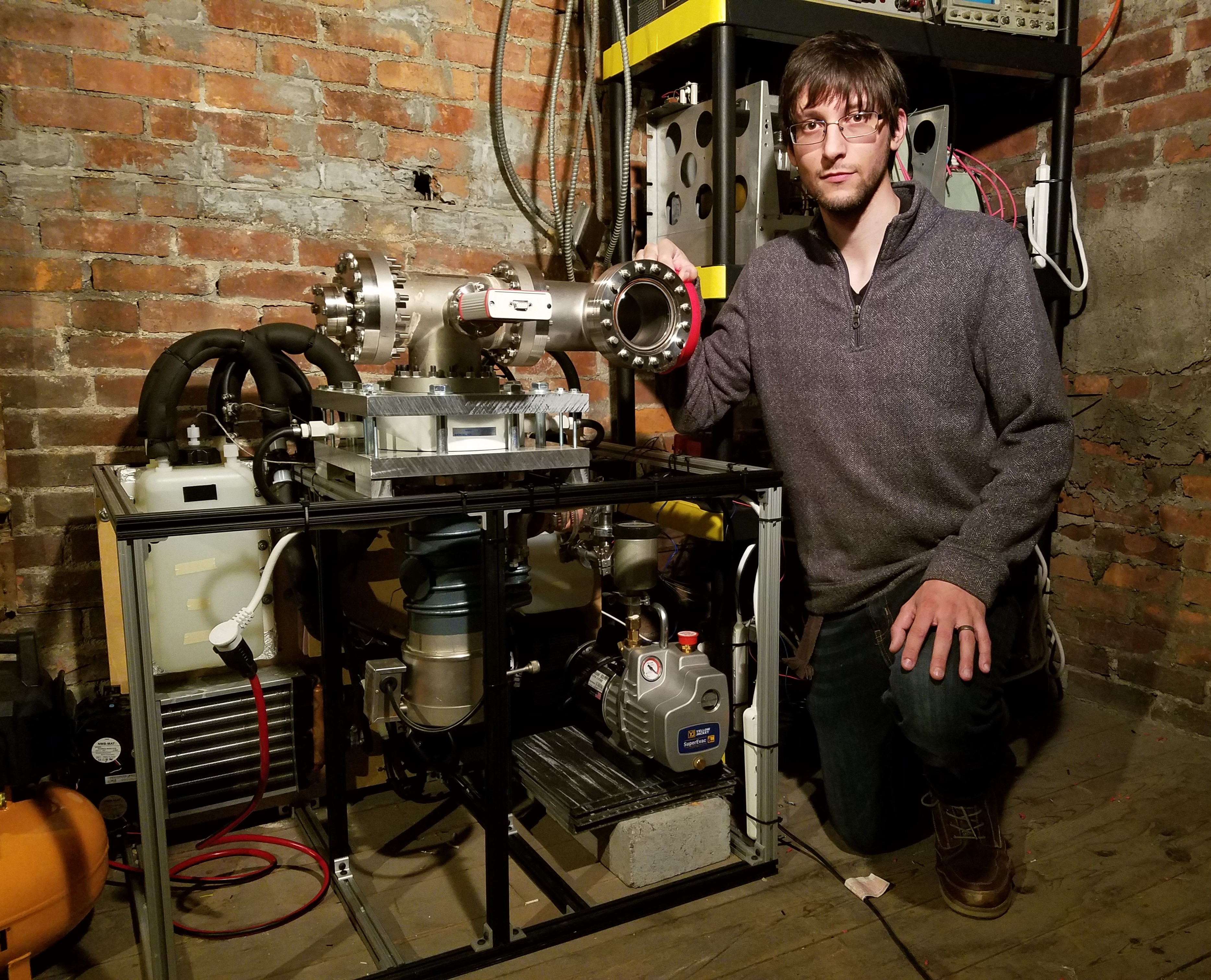
Michael Bretti is designing electric thrusters so that Amateur and Educational microsatellites can maintain or change their orbits. Some of his designs are small enough to work on a PocketQube, a satellite literally so small that it fits in your pocket.
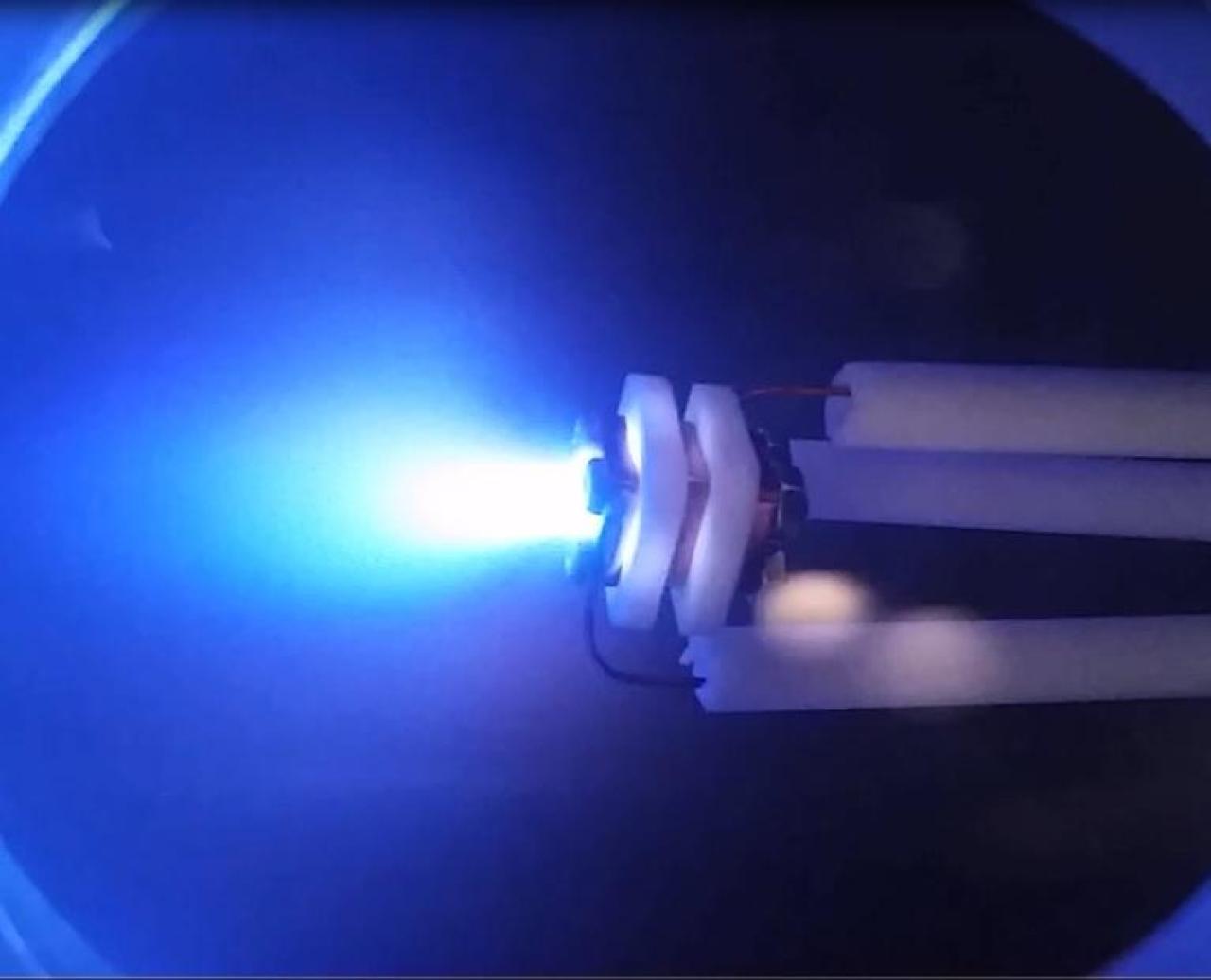
Michael has so far created several working thruster designs, as Open Source Hardware. Below Michael’s photo is his gridded pulsed plasma thruster firing in a vacuum chamber he’s put together in his home. And the photo below that is another of his thruster designs being readied to fly as part of the GENESIS N and L satellites. That’s his thruster between the two measuring tapes.
Michael calls his project Applied Ion Systems, and you can follow his work at @Applied_Ion on Twitter.
I’ve been following Michael’s work for about a year, and this is a tremendously important project for Amateur and Educational satellites. It will provide them with thrusters that are easily affordable on their slim budgets, and allow them to maintain or change their orbits like the big boys!
To test the thrusters, he uses a vacuum chamber that duplicates the hard vacuum of low-earth orbit. Vacuum is hard, and hard vacuum is harder, and hardly cheap. Due to his shoestring budget of literally pocket money – he has no significant funding and works on his own time – Michael’s work has been plagued by failures of his roughing pump. That’s a pump which creates a medium vacuum and supports another pump that provides the space-quality vacuum. He bought and attempted to rebuild a worn-out roughing pump – all that he could afford – but this effort failed. Michael can’t go on with testing until he gets a reliable roughing pump. That would allow him to move forward confidently in creating thrusters for our satellites. Michael would like to buy an Edwards RV12, which is available for no more than $4200 Please help to fund the new pump.
With the ability to achieve a space-quality vacuum again, Michael will proceed with new designs. Not every one succeeds, because space is hard, but enough do. You’ll be able to watch his efforts and – soon enough – perhaps you’ll communicate through some of the satellites he supports.
Shhhhh! That’s the first thing you learn when raising funds for a startup, or running a venture capital fund. You can’t let the common people know! No advertising is permitted, and even publicly discussing the fact that you are collecting funds could get you in trouble with the SEC. But this practice has been obsolete for 7 years, and nobody in the venture capital and startup world seems to know it.
The SEC rule commonly used by startups and VC funds, rule 506(b) of Regulation D, allows them to be exempted from the many reporting and disclosure regulations applied to stocks traded on the market, but at a severe cost: all investors must be accredited, meaning that they must have a degree of sophistication in investment and wealth greater than the common person.
Meant to protect regular people from investments that don’t report enough information to allow them to make a reasoned decision, the other effect of the accreditation requirement is that only rich people can play. You are not allowed to invest in these high-risk, high-reward funds issued by startups and venture capital funds, unless you are wealthy or you yourself are a founder of the business. A net worth of a Million excluding the value of your home, or annual income in excess of $200,000 for an unmarried person and $300,000 common income for a married couple, are required.
Rule 506(b) requires businesses that wish to be exempted from reporting requirements must raise money privately. Advertising for investors is not allowed. They can’t talk about their solicitation of funds to people who aren’t accredited. They can only make solicitations of investors who self-declare themselves as accredited. You’re supposed to have a phone book full of moneybags that you can approach quietly.
This means that startups and venture funds are under severe restrictions of their speech by SEC. You can’t talk about your solicitation for funds where the lowly non-accredited person can hear it. In practice, their lawyers tell them not to publicly discuss anything connected with a fund-raise, or even that their fund exists. Many software companies sell virtual data rooms to shut out the hoi polloi, secure data stores that accredited people can be invited to enter to view and sign documents, while the lowly non-accredited are locked out of that information.
Obviously, this made it difficult for businesses to raise money. So, in 2012, the Jumpstart Our Business Startups Act, or JOBS Act, was passed into law. In the words of SEC, the JOBS act “is intended, among other things, to reduce barriers to capital formation, particularly for smaller companies.” Enacted in 2013 as rule 506(c) of Regulation D, it allows solicitations of capital that are exempted from reporting requirements similarly to rule 506(b), but “general solicitation” that is visible to un-accredited people is allowed, including advertising of the solicitation. Thus, businesses are released from the odious restrictions on speech. The cost of this is that the requirement for accreditation of investors is increased. A fund operating under 506(c) can not just take the world of an investor that they are accredited. They must actively verify it, using tax forms, bank statements, etc.
Fortunately, there are third-party companies that will perform accredited investor verification for as little as $60, and will keep the documents presented by the investor private. Two such companies are:
Use of these companies is advantageous to the investor and the fund, because the fund need never be exposed to the investor’s private documents. They just get a pass or fail report on the investor’s accredited status.
Rule 506(c), to date, is mostly used by real estate funds. Even SEC does not understand why VCs and startups do not use it more. The Director of the SEC’s Division of Corporation Finance, Keith Higgins, said “one wonders why the new Rule 506(c) exemption has not caught on more widely with issuers who have long clamored for the general solicitation ban to be lifted.” There is the additional requirement of validation, with its increased paperwork load on prospective investors, but the effect of this is reduced by using third party validation companies that shield those documents from view, even by the fund that requested validation.
The few negative opinions I’ve gotten from VCs and startup founders, so far, have been focused on aspects of 506(c) that they consider to be problems:
It’s additional paperwork for the investor, and somewhat intrusive paperwork. Your investor will be providing a copy of their tax return and bank documents, or a letter from their fund manager. They don’t have to do that to invest in a 506(b) fund. In a way, I actually consider this a plus. I don’t want the kind of investor who isn’t willing to do a little extra work to get onboard my company.
There is also the issue of democratization of investment. Angels and VCs are about the most entitled people you will meet. But they aren’t the only people with money! Lots of people today meet the standards for accreditation, but their money isn’t currently being utilized effectively, because they aren’t in investment networks with the active angels and VCs. Those who aren’t so entitled, or connected, would be more likely to give my company the attention it deserves. And because 506(c) allows advertising of general solicitations, I can find them.
Another criticism was that it’s too easy to get in trouble with 506(c). For example, if the company that audits your investors for accredited status doesn’t do their job well, you could end up with an unaccredited investor, and (theoretically) be prosecuted for making a “public” offering without the required disclosures and regulation, rather than the private offering you intended. For this reason you should be careful in choosing the company that vettes investors, and the contract you get with them, and they should report to your lawyer. That way, the decision to accept or reject an investor is always based on advice of counsel – which offers additional protections.
Finally, there an innuendo that officers and staff within SEC don’t actually like 506(c), and objected to its passage as law. And that they thus will interpret the law as restrictively as possible, like a cop who looks for ways to ticket you because he doesn’t like your bumper sticker. But this is why we have lawyers and courts.
But for most people, the main objection to 506(c) is that it’s unknown, and relatively new. People like the old ways that they know work. But you get ahead by innovating!
I first encountered rule 506(c) after I had been a partner at OSS Capital for a year. I had felt constrained by the restrictions on speech that fund has under rule 506(b). When I started to found a separate company, the business incubator or “venture studio” Incubator.Fund, I resolved to use rule 506(c), and not simply for the free speech advantages. I have dedicated most of my life to charity, as one of the founders of the Open Source movement in software, and did not have a personal network, a phone book full of moneybags to raise funds from privately, as rule 506(b) assumes. The ability to advertise, using rule 506(c), allows me to reach far beyond my personal network.
Incubator.Fund is doing its initial bootstrap raise in the worst of times: in the middle of the COVID-19 disaster. The bootstrap investors will fund the legal and other work necessary to start the fund and its first incubated companies, and then to solicit for additional limited partners. But because of the awful state of the market (at this writing), I have to sweeten the pot: those bootstrap investors will be offered a portion of the general partner for taking the risk at the worst of times. Maybe that, and the ability to advertise, will be enough to get good investors onboard my company. But without rule 506(c), I doubt we’d have a chance to find them.
To learn more about rule 506(c):
Bruce Perens is one of the founders of the Open Source movement in software. Before that, he helped to create the industry of 3D Character Animated Feature Film at Pixar and its academic predecessor. He is currently general partner at Incubator.Fund and partner at OSS Capital.
I put away a one-year food kit after hurricane Katrina. That was 14 years ago. And a serious hand grain grinder, a portable outdoor wood stove, a Berkey filter to drink from the pool, etc. And I keep and rotate 4 gallons of cooking oil.
I inspected it on February 14th, and replaced two swelled cans, and one 35 lb bucket of beans.
A one year food kit and the other things you should have on hand for a disaster cost thousands, but are not at all out of reach of a middle-class family.
Being responsible means that people need to be able to take care of themselves in a disaster, without being a burden to government resources that should go to those more in need, or will be completely overwhelmed.
The failure of the recent grocery store stock-pilers is not only that they bought at the last minute when resources were scarce for everyone, but that they did not plan in advance and get what they would need, when resources were not scarce.
And I trust that after this, the taint of the gun-nut paranoid prepper will not be attached to more sane people who plan for disaster, as I did.
January 18, 2020
The materials provided are good: heavy and well-machined aluminum, acceptable quality electronic and mechanical components and fasteners. The 3018-PROver is not nearly as “assembled” as the purchasing data indicates. You can download the assembly video or the manual and see for yourself – there are a couple of hours of assembly work, and there will be much consulting of the online manual, the video, and this errata while you are at it. The three major subsystems are mechanically assembled, but have not had the electrical components, wiring and many little parts mounted, and two major subsystems need to be bolted together. And since the instructions leave a lot for you to figure out, if you’re easily frustrated: choose another project.
The PROver version is based on Open Source software and incorporates its own motion controller software: GRBL 1.1. It does not need to be connected to your computer while the router is cutting. Most people will use Open Source CAD software, which does not come with the unit.
There is also a “3018 Pro MX3” version which requires that you purchase the Mach 3 software for $175, has a different main controller board and a different hand controller, and requires a Windows computer to run Mach 3 while the router is cutting. The 3018 PROver is a better choice for most people, as it avoids this expense and complexity. Mach 3 is motion-control software, not the CAD software. You will still need to find that.
The 3018-PROver controller is based on Arduino. The main controller runs the GRBL 1.1 software developed for Arduino and comes with its own hand controller. Hand controllers for other models, like the one for the MX3 version, are not compatible.
Source code for GPL-licensed software in this unit is not on the SainSmart web site as far as I can tell, and it looks like SainSmart still needs to learn how to comply with the licenses to the GPL binary software they distribute, and directly distribute the source code on their own site. I do not know what differences exist from the GRBL 1.1 developer’s source, but I suspect some might exist for the hand controller.
This machine will be covered with chips after operation and will require some wiping down, including passing some sort of wipe inside of the T-slots. I will try to improvise a chip vacuum for mine, no such thing is available to buy.
To find the assembly video, search for Sainsmart Genmitsu CNC Router 3018-PROVer Build. A few hits down from the top of the search on Google, there is a wiki page for the device at wiki.sainsmart.com . You can also find this directly on the wiki, but the indexing is based on SKU numbers. There are assembly videos for other models on Youtube, which you might find helpful.
Most of the tools required for assembly are provided. In addition, you will need a wire cutter to remove two wire ties used as a shipping lock, and a container of light oil to lubricate the lead screws, and some electrical tape to wrap moving wires together.
You will need to download the manual and display it on a big screen. That is the only way you will be able to see the photos adequately to be able to assemble the unit. The photos are in a printed manual provided with the unit, but too small and too low-resolution to tell what you should be doing.
Here are the errata I noted during assembly:
Step 1: You will need to provide your own wire cutter.
Step 2: You are told to mount 6 wire holders, but the photo only shows where two of them go! The video is similarly unhelpful! The second two go on the opposite side, identically to the first two. The third two go on the outside of the frame, on the same side as the stepper motor, opposite the two installed inside.
Step 3: The four wire holders mount on opposite sides of the metal piece. The photos don’t quite show this completely.
Step 5 and 6: The long end of the distance tool is held against the back of the frame, inside the channel. The last slider nut should be against the end of the distance tool. Because of the distance tool, everything lines up well and the 12 bolts go in a lot more easily than I expected.
Step 8: The square projection on the slide nut goes outward.
Step 9: Peel the protective film off of both sides of the acrylic sheets. They are clear, tinted blue, once you do that. Hold the sheet so that it fits the shape of the leg of the Y-Z assembly. That is the correct orientation. Put the bolts through from the outside, and put the slide nuts on the other side by hand, one turn only. Orient the slide nuts horizontally, and then push the acrylic sheet to the channel so that the slide nuts insert into the channel. Turn the bolts, and the slide nuts will seat correctly.
Step 10: There is an error on this page. Where they specify the Y+ and Y- connecting wires, they actually mean X! The VER- numbers are correct, Y should be X.
The main controller is attached to two beams, each of which has four channels. The X- limit switch wire must be run behind the main controller along the top of the bottom beam, looping to the front on the side where the controller has the USB connector. The cover strip goes over the wire on the top channel of the bottom beam.
Step 11: It may be necessary to temporarily remove the wire holders next to the limit switches so that there is enough space to insert the plugs into the limit switch sockets. Put the wire holders back afterward.
Step 13: There are different plugs on each end of the stepper motor wires.
Step 15: By “black cover”, they mean the black plastic nut on the barrel of the emergency stop button. Remove that and the square lock washer. Put the switch into the plate, and then put the lock washer on the switch from the back, with the pointy corners facing the metal plate.
This button is unusual: push to stop, twist to release.
Step 16: Whew! A lot left out here! You are supposed to pass all of the Z wires through a piece of the nylon braided web to protect them from friction. But the piece I was provided, although it can be expanded somewhat, doesn’t expand sufficiently to do this. I wrapped the wires with electrical tape.
Operation
Before you connect the router to your computer, you can play with it using the manual controller. This is non-intuitive though. I noticed that the files included on the SD card would run into hard limits (trip the limit switches) if run with the router starting in the home position. You will have to move X, Y, and Z close to the center of their operation before starting.
The limit switches are confusing. If you are stuck on a limit, which is sure to happen, run the reset function. Move the stuck axis until it stops again – the limit switch will halt the system when it is set, and again when it is cleared! Run the reset function a second time. Then you can move the axis as expected. At this writing I am not sure if configuration will make this easier.